Abstract
In the lead-up to the 2020 U.S. presidential election, we developed tools to monitor the follower dynamics of prominent Twitter users. This work details our investigation into several strange phenomena we observed, which suggest the presence of coordinated manipulation campaigns. We present preliminary evidence of networks of automated (bot) and potentially compromised accounts aiming to artificially inflate or diminish the perceived social status of high-profile individuals. (Note: this work was presented as an extended abstract at IC2S2 2020. It is available as an arXiv preprint but was not submitted as a full peer-reviewed paper.)
Key Contributions
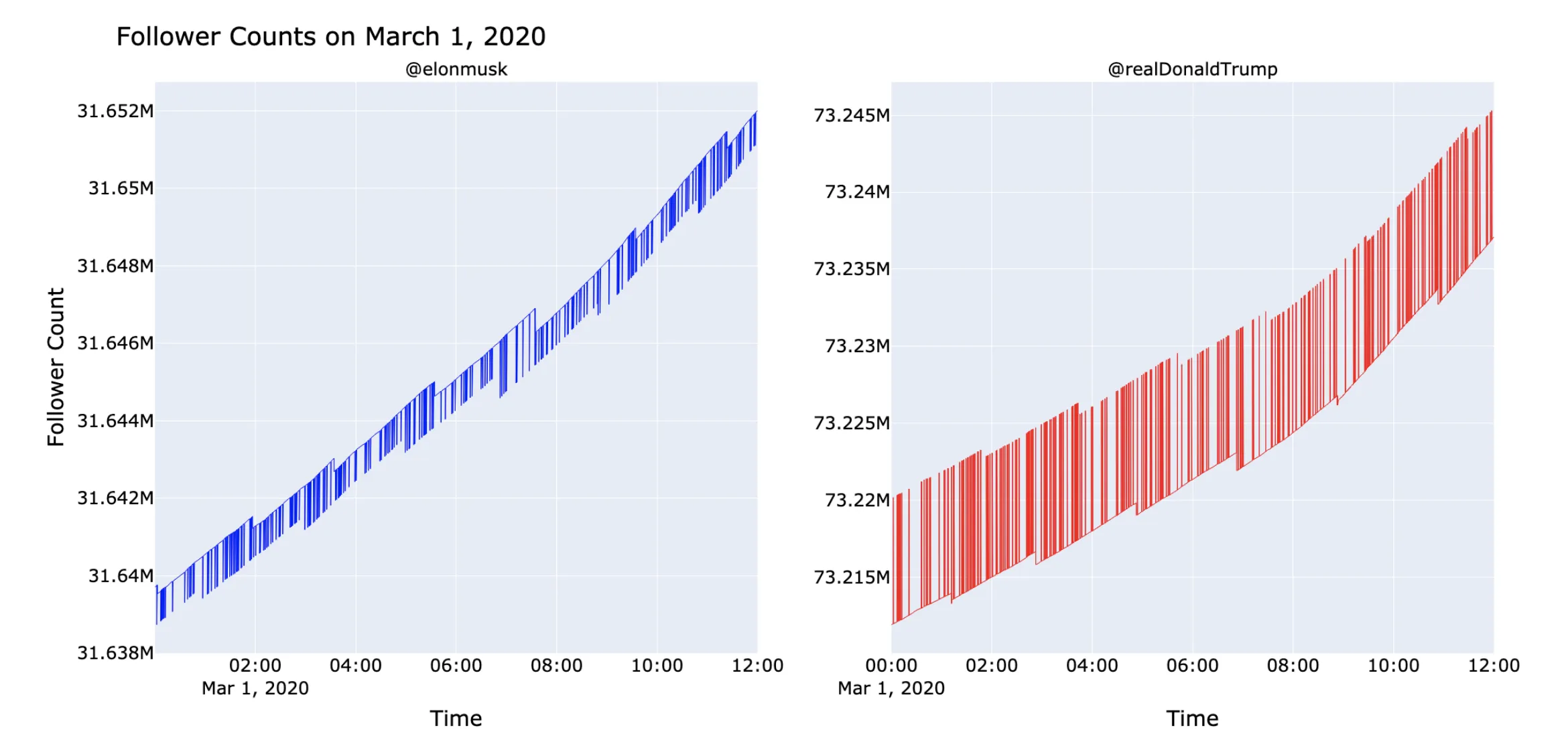
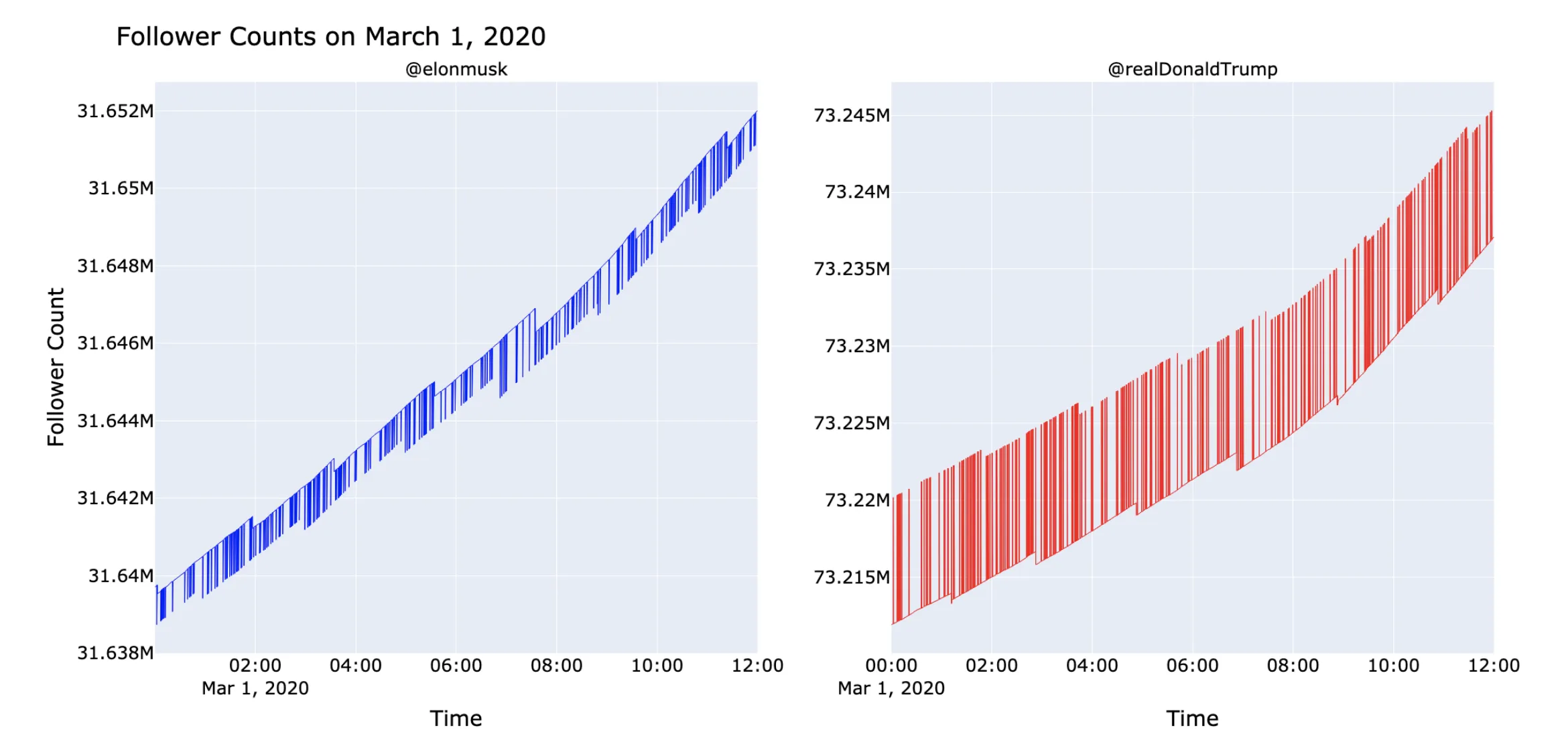
- High-Frequency Sampling Infrastructure: Built custom tooling to sustain 1-second follower-count polling over weeks, implement recursive follower-list “tunneling” through Twitter’s pagination limits, and manage API rate windows, capturing sub-minute temporal signatures invisible to standard API sampling
- Novel Detection Methods: Developed monitoring tools to capture sub-second follower dynamics and identify anomalous patterns in high-profile Twitter accounts
- Comprehensive Phenomenon Documentation: Systematically catalogued four distinct types of coordinated manipulation: spikes & sawteeth, circulating accounts, resurrected ancient accounts, and follower list anomalies
- Observational Framework: Created an observational methodology designed to characterize manipulation phenomena without requiring internal platform access
- Preliminary Evidence of Coordination: Documented anomalous patterns consistent with systematic bot networks targeting prominent political figures during the 2020 election period
Methodological Strategy
To capture these transient phenomena, we engineered a high-frequency observational pipeline that bypassed standard sampling limitations. Our framework treated the social graph as a dynamic signal:
- High-Resolution Sampling: Implemented “cycling scripts” to monitor follower counts at 1-second resolution, revealing sub-minute “spike” anomalies often missed by aggregate metrics
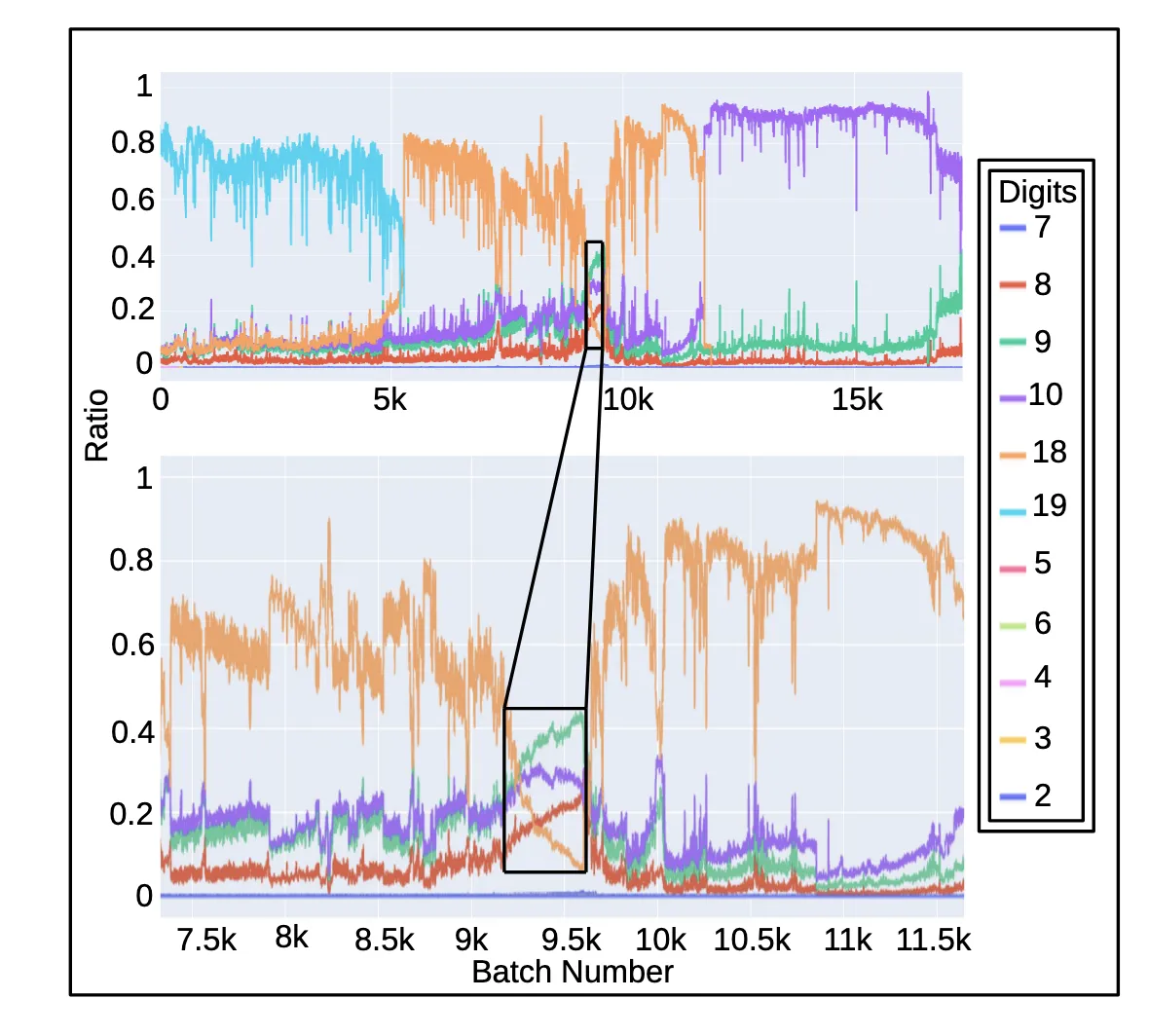
- Recursive “Tunneling”: Developed a recursive sampling method to extract deep history from follower lists, uncovering strata of “ancient” accounts buried by recent activity
- Cross-Referencing: Correlated circulation events with follower count distortions to validate the “sawtooth” waveform hypothesis
Engineering Note: This methodology required custom infrastructure to work around Twitter API rate limits and pagination constraints. We built a distributed “tunneling” system that recursively paginated through follower lists (which Twitter caps at 5,000 per request) while respecting rate windows. The “cycling scripts” maintained persistent connections and implemented intelligent backoff strategies to sustain continuous 1-second polling over weeks of observation. This data engineering work was essential to capturing the high-resolution temporal signatures that standard API usage would miss.
Key Findings
- Spikes & Sawteeth: Dramatic, sub-second spikes and saw-tooth wave patterns in follower counts, suggesting automated activity
- Circulating Accounts: Cohorts of users repeatedly following and unfollowing the same high-profile accounts
- ‘Resurrected’ Ancient Accounts: Disproportionate numbers of pre-2010 Twitter accounts with long inactivity periods suddenly appearing as recent followers
- Follower List Anomalies: Unusual temporal groupings in follower histories suggesting historical manipulation campaigns
Significance & Sociological Impact
Beyond the technical detection of botnets, this work raises questions about a potential vulnerability in the infrastructure of modern public discourse. The observed patterns suggest these coordinated campaigns may be targeting the metrics that algorithms use to verify relevance (such as follower counts and engagement rates) as a vector for artificially shifting perceived social proof.
- Distortion of Democratic Signals: Our observations are consistent with attempts to manipulate the “rich-get-richer” dynamics of social platforms. If inorganic follower inflation can influence recommender systems, that could amplify specific narratives to legitimate users. This remains a documented observation rather than a proven causal chain, and warrants further investigation.
- Platform Weaponization: The data highlights patterns where “ancient” dormant accounts appear as new followers in bulk, suggesting that account-age filters may be insufficient on their own as a defense against coordinated manipulation.
- A Case for Metric Scrutiny: These findings suggest that raw follower counts are noisy signals that can be manipulated at scale. Supplementing them with engagement-quality metrics may make platform recommender systems more robust to coordinated inorganic activity.
Citation
@article{heidenreich2020investigating,
title={Investigating Coordinated 'Social' Targeting of High-Profile Twitter Accounts},
author={Heidenreich, Hunter Scott and Mujib, Munif Ishad and Williams, Jake Ryland},
journal={arXiv},
volume={abs/2008.02874},
year={2020},
url={https://arxiv.org/abs/2008.02874},
eprint={2008.02874},
eprinttype={arXiv}
}
Related Work
For related work in the computational social science cluster:
- NewsTweet Dataset: Social Media in Digital Journalism: a companion dataset studying how tweets surface in journalism, from the same research group and time period.
- Look, Don’t Tweet: Unified Data Models for Social NLP: provides the unified cross-platform social media data model used in broader analysis of Twitter and related platforms.
- GPT-2 Susceptibility to Universal Adversarial Triggers: proposes UAT-based bot detection as a constructive application, addressing the same automated manipulation behavior documented here from a complementary detection angle.